Find out the key of any Wi-Fi connection
If you have forgotten the password that you use to connect to the Internet using a Wi-Fi connection, you can "reset" the router or use an application like Aircrack-ng to find it out. Although this isn't what most users use this application for.
Discover the passwords of wireless networks
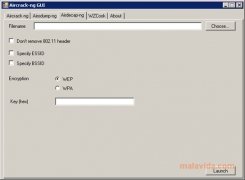
Aircrack-ng is part of a group of applications known as packet sniffers, this means, it's an application that intercepts and logs data streams that flow across a network. It will let the user recover the WEP and WPA-PSK key from any wireless connection based on the IEEE 802.11 standard. To manage this, it has a group of tools like airbase-ng, aircrack-ng, airodump-ng, ..., each of these for a specific task.
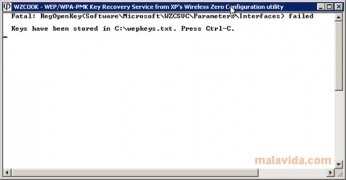
The method implemented by Aircrack-ng is called an FMS attack, receiving this name in honor of Fluhrer, Mantin and Shamir that were the first to demonstrate the weakness of WEP ciphering. Furthermore, it includes improvements made to KoreK and others.
To find out the passwords of wireless networks that aren't properly protected, Aircrack-ng captures the first packages that are transmitted by a connection, allowing the user to obtain the passwords and use them to connect to the Internet. The use of Aircrack-ng requires advanced network knowledge.
Requirements and additional information:
- Requires the users to create their own DLLs to connect the application with the wireless card.
 Vanessa Martín
Vanessa Martín
¡Hi! I am Vanessa Martin, I like to travel, music, photography, and I am passionate about the Internet, as it is a great source of information where you can find everything you need. If it exists, it is on the Internet. Another of my great...

Antony Peel