Check the security of your network with this pentesting app
Hijacking in computer jargon comes to refer to any technique that by illegal methods seeks to attack a network or user in order to own something. It applies to the theft of information, the hijacking of network connections, modems...
Test your networks for penetration
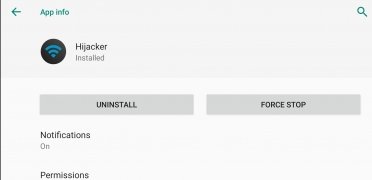
This application called Hijacker is a tool to carry out attacks of this type, although as it is developed from an ethical point of view, we will say that it is to execute penetration tests or pentesting. That is why through a usable and intelligible user interface offers different functions to carry them out.
These are the main features offered by this app:
- Compilation of information about access points and clients around, activity of a specific network, statistics of access points and stations, data of the manufacturer of the device, signal strength of the devices ...
- Deauthentication attacks of all clients of a network or of a specific one, MDK3 Beacon Flooding, DoS,...
- Copying commands and MAC addresses.
- Commands to enable and disable automatic monitoring.
- Sorting and filtering of access points and stations with many parameters.
- Exporting the collected information to a file.
Requirements and additional information:
- Requires a rooted device.
- Although some antivirus indicate it as malware, the application does not pose any danger. It is marked by the nature of its functions.
- Minimum operating system requirements: Android 5.0.
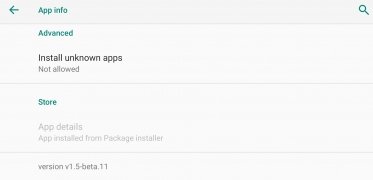
- The installation of the app by means of the APK file requires the activation of the "Unknown sources" option within Settings>Applications.
 Elies Guzmán
Elies Guzmán
With a degree in History, and later, in Documentation, I have over a decade of experience testing and writing about apps: reviews, guides, articles, news, tricks, and more. They have been countless, especially on Android, an operating system...

Shay O’Toole